If the words of a 12-word seed phrase are known, it’s deceptively easy to enter the wallet and sweep the funds.
A system architect managed to break a seed phrase and claimed a 100,000 Satoshi reward, equivalent to 0.001 Bitcoin or $29, in less than 30 minutes. Cointelegraph interviewed Andrew Fraser from Boston, who emphasized the importance of keeping a Bitcoin wallet seed phrase safe and offline.
A seed phrase, also known as a recovery phrase, consists of a series of random words generated when a wallet is created, acting like a master key to access the wallet. Fraser successfully brute-forced a 12-word seed phrase that Bitcoin educator “Wicked Bitcoin” had posted on Twitter:
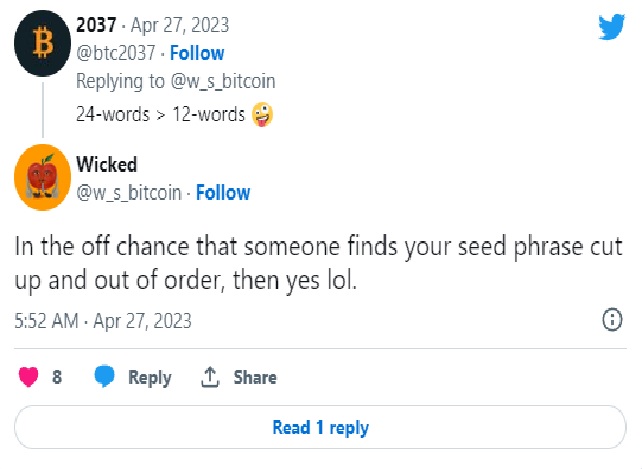
As demonstrated, Wicked’s Tweet posed a challenge for users to figure out the correct sequence of the 12-word seed phrase.
“Anyone wants to try and brute force this 12-word seed phrase securing 100,000 sats? I’ll give you all 12 words but in no particular order. Standard derivation path m/84’/0’/0’…no fancy tricks. GL.”
It took a mere 25 minutes to unlock the 100,000 satoshis, valued at just below $30. This incident serves as a pertinent reminder for Bitcoin users and crypto enthusiasts to prioritize crypto security.
Fraser managed to crack the code using BTCrecover, a software application accessible on GitHub. The software provides an array of tools that can identify seed phrases with missing or jumbled mnemonics, as well as passphrase-cracking utilities. Fraser shared with Cointelegraph via Twitter DMs:
He pointed out that anyone with basic knowledge of executing Python scripts, using the Windows command shell, and understanding the Bitcoin protocol—especially BIP39 mnemonics—should be able to reproduce his achievement.
Cointelegraph asked Fraser about the security of 12-word seed keys. Fraser clarified that they are “perfectly secure if the words remain unknown to an attacker or if a passphrase ’13th seed word’ is used in the wallet’s derivation path.”
Additionally, he stressed the enhanced security offered by 24-word seed keys.
Fraser broke down the entropy calculations to illustrate the difference in security between the two types of seed keys. A 12-word seed has around 128 bits of entropy, while a 24-word seed features 256 bits. When an attacker knows the unordered words of a 12-word seed, there are only about half a billion potential combinations, which can be relatively easily tested with a decent GPU. In contrast, a 24-word seed has approximately 6.24^24 possible combinations — and that number has a lot of zeros.
The likelihood of an attacker successfully cracking a 12-word seed phrase is extremely low. Although a 24-word seed phrase offers superior security, as Wicked pointed out in a follow-up analysis of the seed phrase challenge, “it’s not going to be hacked, to be honest.”
In the end, this serves as a timely reminder for everyone to ensure seed phrases are never posted or shared online. This means seed phrases should not be stored in password managers or cloud storage solutions, and they definitely should not be typed into a phone.
Source: https://cointelegraph.com/news/bitcoin-advocate-cracks-known-12-word-seed-phrase-in-minutes